-
TRANSDUCERS
- TRANSDUCERS
-
BASIC COMPONENTS DK
- BASIC COMPONENTS DK
-
MARKETPLACE
- MARKETPLACE
-
DEVELOPMENT BOARDS & KITS
- DEVELOPMENT BOARDS & KITS
-
CABLE ASSEMBLIES
- CABLE ASSEMBLIES
-
RF AND WIRELESS
- RF AND WIRELESS
-
BOXES ENCLOSURES RACKS
- BOXES ENCLOSURES RACKS
-
AUDIO PRODUCTS
- AUDIO PRODUCTS
-
ARTILA
- ARTILA
-
FANS-BLOWERS-THERMAL MANAGEMENT
- FANS-BLOWERS-THERMAL MANAGEMENT
-
WIRELESS MODULES
- WIRELESS MODULES
-
TERMINALS
- TERMINALS
-
Cables/Wires
- Cables/Wires
-
SINGLE BOARD COMPUTER
- SINGLE BOARD COMPUTER
-
BREAKOUT BOARDS
- BREAKOUT BOARDS
-
LED
- LED
-
TEST AND MEASUREMENT
- TEST AND MEASUREMENT
-
POTENTIONMETERS AND VARIABLE RESISTORS
- POTENTIONMETERS AND VARIABLE RESISTORS
-
DEVELOPMENT BOARDS AND IC's
- DEVELOPMENT BOARDS AND IC's
-
EMBEDDED COMPUTERS
- EMBEDDED COMPUTERS
-
OPTOELECTRONICS
- OPTOELECTRONICS
-
INDUSTRAL AUTOMATION AND CONTROL
- INDUSTRAL AUTOMATION AND CONTROL
-
COMPUTER EQUIPMENT
- COMPUTER EQUIPMENT
-
CONNECTORS & INTERCONNECTS
- CONNECTORS & INTERCONNECTS
-
MAKER/DIY EDUCATIONAL
- MAKER/DIY EDUCATIONAL
-
TOOLS
- TOOLS
-
MOTORS/ACTUATORS/SOLEENOIDS/DRIVERS
- MOTORS/ACTUATORS/SOLEENOIDS/DRIVERS
-
FPGA HARDWARE
- FPGA HARDWARE
-
POWER SUPPLIES
- POWER SUPPLIES
-
ROBOTICS & AUTOMATION
- ROBOTICS & AUTOMATION
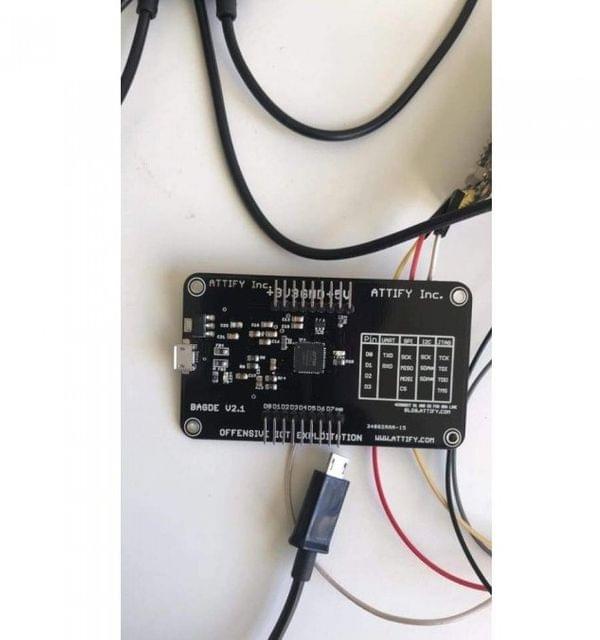
Description
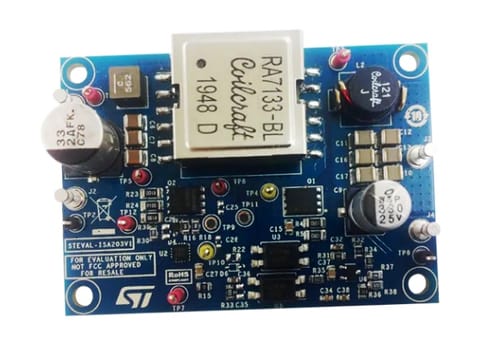
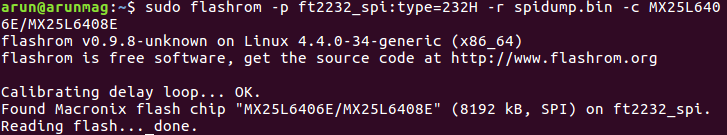
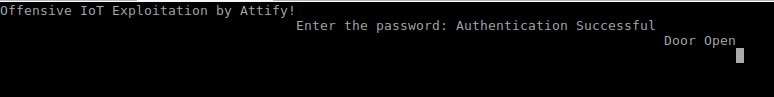
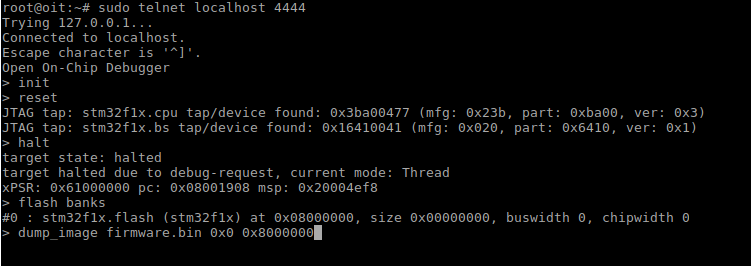
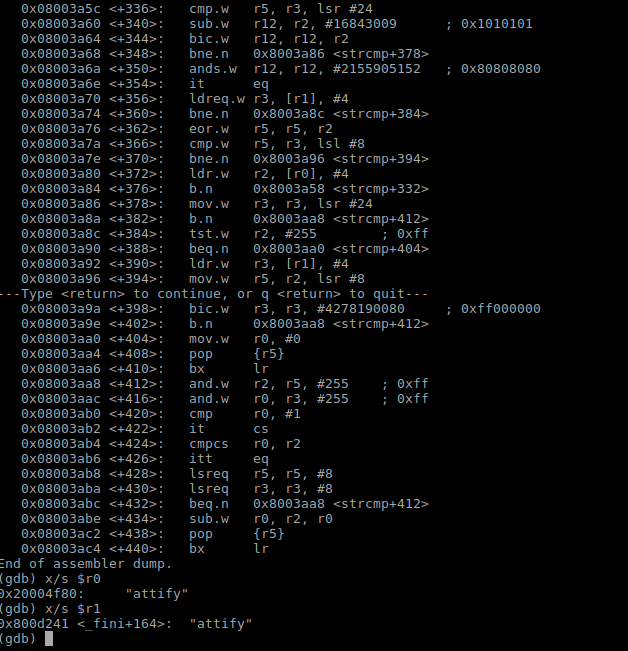
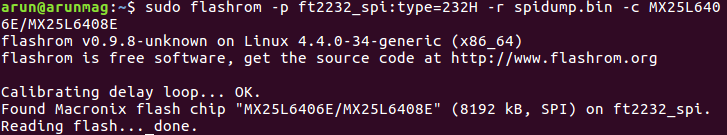
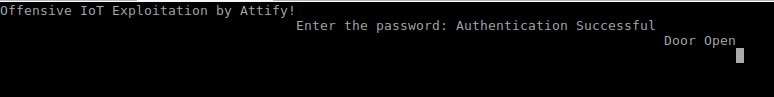
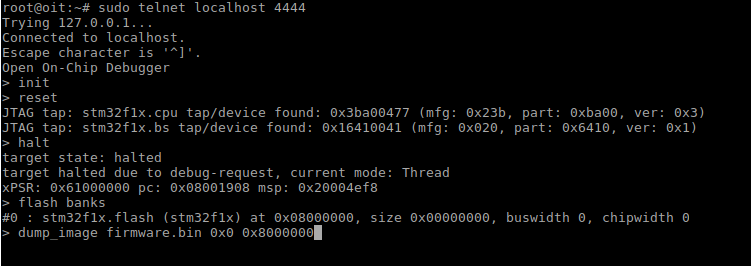
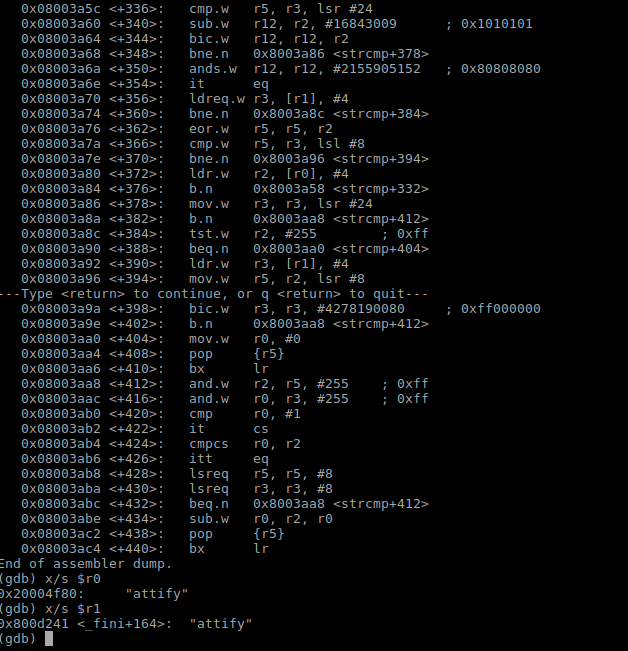
Attify badge is a hardware tool that allows you to interact with various hardware interfaces and ports such as UART, SPI, I2C, JTAG, GPIO and so on.
- Look for a 4 or 3 pins or pads which are in a block together.
- In order to perform UART based exploitation, we need to correctly identify four pins namely – Tx, Rx, GND and Vcc.
- To identify the individual pins, a multi-meter is required. Start off by connecting the black probe and the red probe of the multimeter to the device GND and the ground pin of Attify badge respectively. Reiterate till you hear a beep sound.
- VCC can be ignored for our case, since it is not needed for a UART based exploitation.
- By using a multimeter as ohmmeter, an infinite resistance between the TX and VCC pin will be noticed. This can also be determined by a huge variation or fluctuation in the voltage as soon as we power on the device.
- Rx can be determined by the pin having the lowest voltage during the entire process, with having the black probe connected to the GND of the Attify badge.
- Home
- DEVELOPMENT BOARDS AND IC's
- Attify Badge - UART, JTAG, SPI, I2C
Attify Badge - UART, JTAG, SPI, I2C
SIZE GUIDE
- Out of Stock. Call us before placing an order.
Description of product
Description
Attify badge is a hardware tool that allows you to interact with various hardware interfaces and ports such as UART, SPI, I2C, JTAG, GPIO and so on.
- Look for a 4 or 3 pins or pads which are in a block together.
- In order to perform UART based exploitation, we need to correctly identify four pins namely – Tx, Rx, GND and Vcc.
- To identify the individual pins, a multi-meter is required. Start off by connecting the black probe and the red probe of the multimeter to the device GND and the ground pin of Attify badge respectively. Reiterate till you hear a beep sound.
- VCC can be ignored for our case, since it is not needed for a UART based exploitation.
- By using a multimeter as ohmmeter, an infinite resistance between the TX and VCC pin will be noticed. This can also be determined by a huge variation or fluctuation in the voltage as soon as we power on the device.
- Rx can be determined by the pin having the lowest voltage during the entire process, with having the black probe connected to the GND of the Attify badge.
NEWSLETTER
Subscribe to get Email Updates!
Thanks for subscribe.
Your response has been recorded.
INFORMATION
ACCOUNT
ADDRESS
Tenet Technetronics# 2514/U, 7th 'A' Main Road, Opp. to BBMP Swimming Pool, Hampinagar, Vijayanagar 2nd Stage.
Bangalore
Karnataka - 560104
IN
Tenet Technetronics focuses on “Simplifying Technology for Life” and has been striving to deliver the same from the day of its inception since 2007. Founded by young set of graduates with guidance from ardent professionals and academicians the company focuses on delivering high quality products to its customers at the right cost considering the support and lifelong engagement with customers. “We don’t believe in a sell and forget model “and concentrate and building relationships with customers that accelerates, enhances as well as provides excellence in their next exciting project.